Obfuscation
Obfuscation refers to the practice of making something unclear or difficult to understand. In the context of software, it usually means taking code and transforming it in such a way that it becomes hard for people to read or understand, even though it still works the same way.
Role in proprietary software
Proprietary software often relies on obfuscation as a deliberate strategy to "protect" their code, making it challenging for developers, researchers, and security experts to innovate, ensure transparency, verify functionality, and guarantee security.
An example
Original Code
Consider this code sample:
// Returns the sum of a + b
function add(a, b) {
return a + b;
}
console.log(add(5, 3)); // Outputs: 8
This Javascript code is clear and readable. It takes two parameters, a and b and returns their sum.
Obfuscated code
After obfuscation, the code now looks like this:
function add(_0x1c33ee, _0x156530) {
var _0x3b278d = (function () {
var _0x59f22f = !![];
return function (_0x437cb0, _0x2043ee) {
var _0x47c588 = _0x59f22f
? function () {
if (_0x2043ee) {
var _0x36aef = _0x2043ee["apply"](_0x437cb0, arguments);
return (_0x2043ee = null), _0x36aef;
}
}
: function () {};
return (_0x59f22f = ![]), _0x47c588;
};
})(),
_0x791f9c = _0x3b278d(this, function () {
var _0x565167;
try {
var _0x3e59b2 = Function(
"return\x20(fu" +
"nction()\x20" +
("{}.constru" + "ctor(\x22retu" + "rn\x20this\x22)(" + "\x20)") +
");"
);
_0x565167 = _0x3e59b2();
} catch (_0x46039f) {
_0x565167 = window;
}
var _0x5a4537 = (_0x565167["console"] = _0x565167["console"] || {}),
_0x312085 = [
"log",
"warn",
"info",
"error",
"exception",
"table",
"trace",
];
for (
var _0x4aaa46 = 0xb38 * -0x2 + -0x3e9 + 0x1 * 0x1a59;
_0x4aaa46 < _0x312085["length"];
_0x4aaa46++
) {
var _0x3cd5de =
_0x3b278d["constructo" + "r"]["prototype"]["bind"](_0x3b278d),
_0x55a3b4 = _0x312085[_0x4aaa46],
_0x59a729 = _0x5a4537[_0x55a3b4] || _0x3cd5de;
(_0x3cd5de["__proto__"] = _0x3b278d["bind"](_0x3b278d)),
(_0x3cd5de["toString"] = _0x59a729["toString"]["bind"](_0x59a729)),
(_0x5a4537[_0x55a3b4] = _0x3cd5de);
}
});
return _0x791f9c(), _0x1c33ee + _0x156530;
}
console["log"](
add(0x3 * -0x1b2 + 0x1d7e + -0x1863, -0x2 * 0x1029 + 0x2621 * 0x1 + -0x5cc)
);
The obfuscated code is difficult to read and contains complicated variable names like _0x55a3b4 or _0x59a729. The code structure is complex and contains nested functions and conditions. The last line even contains contains multiple mathematical operations!
Still, both code samples output the same result:
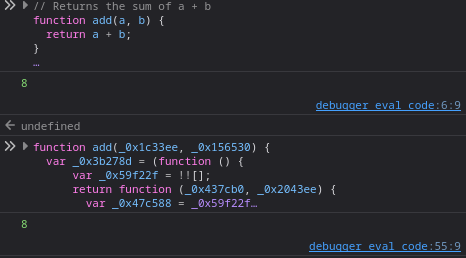
Need proof?
If you are unfamiliar with this practice, it may be hard to believe!
If you are on a desktop browser, press Ctrl + Shift + I and navigate to the 'Console' tab. Then, simply paste the code samples into it.